Your Cart is Empty
Customer Testimonials
-
"Great customer service. The folks at Novedge were super helpful in navigating a somewhat complicated order including software upgrades and serial numbers in various stages of inactivity. They were friendly and helpful throughout the process.."
Ruben Ruckmark
"Quick & very helpful. We have been using Novedge for years and are very happy with their quick service when we need to make a purchase and excellent support resolving any issues."
Will Woodson
"Scott is the best. He reminds me about subscriptions dates, guides me in the correct direction for updates. He always responds promptly to me. He is literally the reason I continue to work with Novedge and will do so in the future."
Edward Mchugh
"Calvin Lok is “the man”. After my purchase of Sketchup 2021, he called me and provided step-by-step instructions to ease me through difficulties I was having with the setup of my new software."
Mike Borzage
Design Software History: CAD Ethics and Data Governance: From Geometric Kernels to Lifecycle Provenance
February 27, 2026 13 min read
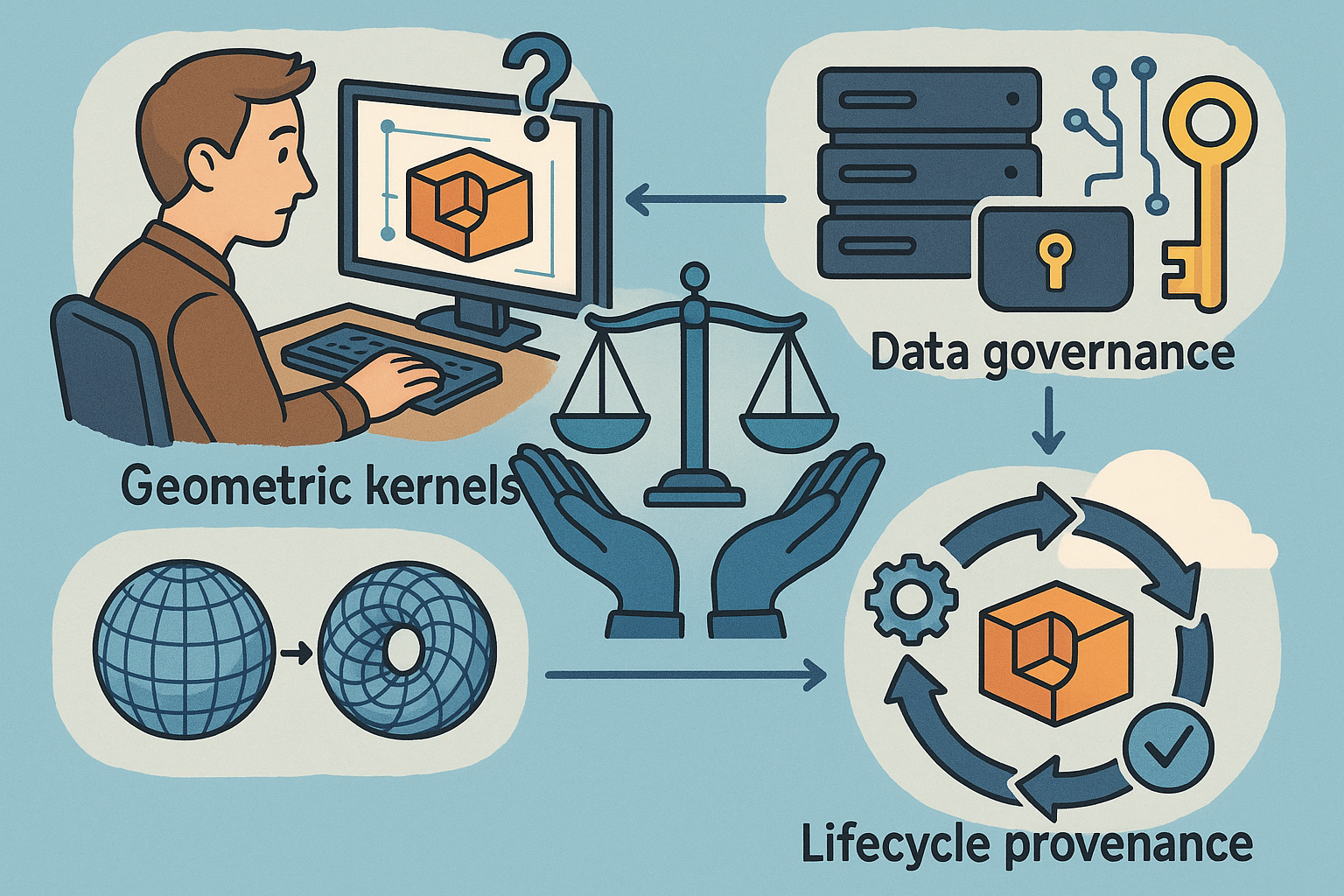

Why CAD Ethics and Data Governance Matter
From geometry to lifecycle context: the real scope of design data
The commonly cited trio of B-reps, meshes, and NURBS captures only a fraction of what modern toolchains manage. In contemporary product and building pipelines, the authoritative digital record spans geometric kernels (Parasolid in Siemens NX, CGM in Dassault Systèmes CATIA, ShapeManager in Autodesk Inventor, and Open Cascade Technology in open ecosystems), plus richly structured PMI/MBD semantics defined under standards such as ASME Y14.41 and ISO 16792. To that core, engineers attach analysis-ready discretizations, solver decks, and surrogate models across FEA, CFD, and systems simulation, linking them back to geometric features to make model updates auditable, reproducible, and traceable. The same product record accumulates material specifications, additive/subtractive process parameters, inspection plans, and nonconformance dispositions, each carrying effectivity windows and configuration baselines. Downstream, the record extends to NC toolpaths, build orientations for powder-bed fusion, machine parameters, and even environmental controls for composite cure cycles. Product lifecycle management systems—ENOVIA on the 3DEXPERIENCE platform, Siemens Teamcenter, PTC Windchill, Aras Innovator, Autodesk Vault and Autodesk Construction Cloud—attach suppliers, quality data, and service bulletins, while requirements interchange via ReqIF keeps verification matrices synchronized. Crucially, that “single model” is now accompanied by provenance: who authored which feature, on which version of the kernel, with what tolerancing scheme, and under what change request. Digital signatures, cryptographic hashes, and context-rich activity logs serve as the connective tissue. In practice, “design data” is a stack: geometric definition; semantic annotations; multiphysics assumptions; manufacturing intent; test evidence; and product-as-operated feedback. Ethical governance, therefore, must treat this entire stack—its creation, sharing, and evolution—as the object of care, not just the rendered shape that first comes to mind.Ethical fault lines where design intent meets real-world consequences
The ethical stakes sharpen when geometry becomes hardware. Safety and accountability sit first among equals: a flawed tolerance stack-up or misinterpreted datum scheme can propagate through suppliers and into the field, where failure modes carry human and environmental risk. The authority model—which object is the master, who can change it, and how changes propagate—anchors accountability. Privacy and sovereignty follow, as CAD and PLM increasingly store personally identifiable information from scans (dentistry, prosthetics, building digitization) and asset-level telemetry. When data moves to multi-tenant clouds, regional laws such as GDPR and evolving interpretations post-Schrems II demand careful residency, encryption, and access logging strategies. Intellectual property protection is an enduring pressure point in distributed supply chains. Tooling vendors like Dassault Systèmes, Siemens, PTC, Autodesk, and Aras have all expanded right-management, watermarking, and redaction features because a leaked assembly model can erase competitive advantage overnight. Export controls and dual-use considerations compound the challenge; the same topology-optimized bracket design or high-strength polymer formulation could be subject to ITAR/EAR constraints if integrated into defense or critical-infrastructure systems. Finally, longevity and trust hinge on long-term archiving: if your digital twin cannot be reconstructed 20 years from now to investigate a safety event or warranty claim, governance has failed. LOTAR-aligned policies exist precisely to prevent such amnesia, insisting on neutral encodings, validation properties, and migration plans that preserve meaning, not merely files. Ethics in CAD is thus not a soft add-on; it is the set of guardrails that keeps intent, accountability, and law in alignment across a model’s journey from whiteboard to fielded service. It is where duty-of-care, privacy, and sovereignty meet branch protection rules, schemas, and file formats.Business-critical stakes and the actors shaping the rules
The operational stakes are brutally practical. Organizations wrestle with single source of truth versus shadow copies as email attachments, desktop exports, and unmanaged supplier mirrors lead to version drift. Interoperability teeters between proprietary richness and neutral portability: STEP AP242 and JT Open promise resilient exchange and visualization-with-rights, but companies must weigh the loss of kernel-native behaviors against policy-mandated durability. Cloud versus on-prem decisions are framed not only by cost and agility, but also by GDPR, Schrems II, CCPA, ITAR/EAR, DFARS, and NIST SP 800-171/172 constraints; region pinning, customer-managed keys, and sovereign cloud options are becoming table stakes. Key actors are making those trade-offs concrete. Dassault Systèmes positions 3DEXPERIENCE as an end-to-end governance fabric; Siemens Digital Industries Software ties NX, Teamcenter, and Active Workspace into verifiable workflows; PTC threads Creo and Windchill through digitally signed eBOM/mBOM transitions; Autodesk integrates Fusion 360, Inventor, Revit, and Vault/ACC around collaborative controls; Aras Innovator’s open architecture attracts enterprises seeking model-based configuration without heavy lock-in; Open Cascade anchors open-source alternatives in the kernel space. On the standards and consortium front, ISO (STEP AP242, AP239/PLCS), ASME Y14.41, LOTAR International, ProSTEP iViP, PDES, Inc., and NIST drive technical consensus and test programs. Industry voices—Bernard Charlès, Tony Hemmelgarn, Jim Heppelmann, Andrew Anagnost, and Jon Hirschtick—shape narratives around openness, SaaS delivery, and model-based enterprise. The throughline: governance is not merely compliance; it is the enablement layer that turns collaborative design from a security liability into a competitive advantage.Historical Incidents that Reshaped Policy and Practice
Digital mock-up as authority and the PLM turn
The early-to-mid 1990s marked a pivotal shift when Boeing executed the 777 with a fully digital program in CATIA, foreshadowing the modern concept of digital mock-up (DMU) as master authority. Eliminating physical mock-ups at that scale forced a rethinking of ownership and configuration control: the CAD model, not paper drawings, would dictate as-designed truth across structures, systems, and interiors. That singular choice cascaded into new policies for supplier engagement. Access to the authoritative model had to be metered by role and effectivity; engineers needed governed branches, and suppliers required scoped visibility with traceability of what they viewed and when. The company learned to formalize authoring domains: which organization controlled which model space, how conflicting changes were resolved, and how baselines were captured for certification and airworthiness documentation. The lessons introduced the discipline that later hardened into PLM-era governance. Vendors responded with platforms that wrapped CAD with workflow, state machines, and change records. ENOVIA matured as the orchestration layer for CATIA data; Teamcenter and Windchill framed similar approaches for NX and Pro/ENGINEER/Creo. Crucially, DMU authority challenged the drawing-centric mindset: PMI had to be embedded in 3D, and toolchains needed to communicate semantics, not just tessellations. Boeing’s rigor encouraged the subsequent standardization push—ASME Y14.41 for digital product definition and the evolution of STEP to carry managed model-based data. The DMU moment taught a durable lesson: when the model becomes the contract, ethics and data governance cease to be back-office concerns; they become the airworthiness of the digital thread itself.- Authority requires clear rules of control and effectivity, not just file naming.
- Supplier access must be granular, audited, and revocable without disrupting schedules.
- Semantic PMI is essential when the model replaces drawings as the legal instrument.
- PLM matures from vaulting to process governance when DMU is the master.
Interoperability and metadata failures that redefined rigor
A decade later, the Airbus A380 wiring harness crisis exposed what happens when authority models fragment across tool versions and sites. CATIA V4 and V5 data mismatches, incomplete conversions, and translation gaps left harness routing inconsistent with the as-built geometry, forcing painful rework and multi-year delays. The governance consequences were swift and enterprise-wide: mandates for version alignment, supplier tool certification, and the principle that if multi-CAD must exist, then neutral, semantic exchanges—AP242 with validation properties—become obligatory. Companies learned to verify not just whether a file opens, but whether feature intent, layer semantics, units, and tolerances survive the round trip. What looked like an “interoperability” problem was, at its core, a policy failure: authority and conformance had not been tightly defined. A related lesson arrived from space exploration. The 1999 loss of NASA’s Mars Climate Orbiter traced back to a unit mismatch in the tool chain, highlighting the danger of silent assumptions. Engineering responded by tightening metadata governance, verified requirements flow-down, and “unit and reference frame” checks baked directly into CAD/CAE workflows. Sign-offs became more explicit; configuration states carried meta-assertions about measurement systems and solver settings; and testable gates were placed before design changes could propagate. Together, these events catalyzed a shift to automated conformance checking. The industry embraced model verification scripts, PMI-driven GD&T validators, and AP242 validation properties to detect discrepancies before they metastasize. The culture widened beyond “can we share geometry?” to “can we prove what this data means, and that it will still mean that after we move it?”- Version alignment is a governance policy, not a courtesy.
- Validation properties in STEP AP242 are essential for round-trip trust.
- Units, frames, and tolerances must be machine-verifiable metadata at gates.
- Supplier certification should include toolchain conformance and data health checks.
IP, export, cyber, sovereignty, and community norms under stress
Security and law reshaped CAD governance in the 2010s. The Waymo v. Uber litigation over alleged LiDAR design exfiltration put a spotlight on insider risk. Enterprises accelerated deployment of data loss prevention tailored to CAD, adopting zero-trust access, granular view-only sharing, and forensic audit trails that log feature opens, exports, and model derivatives. PLM systems evolved to record the lineage of assemblies and to watermark viewables so investigators could trace leaks. Parallel to insider threats, high-profile intrusions across defense supply chains drove U.S. policy: DFARS 252.204-7012, NIST SP 800-171/172, and the emergence of CMMC connected cybersecurity hygiene directly to eligibility for contracts, forcing contractors to prove how they store, share, and audit CUI-laden CAD data. Export controls and platform governance marched in lockstep. The Defense Distributed saga—publishing 3D-printed firearm CAD—pitched open repositories and code hosting platforms into the ITAR/EAR arena. Communities like Thingiverse and GitHub sharpened moderation, geofencing, and takedown paths, while design forums refined licensing and derivative-use policies. Sovereignty concerns swelled under GDPR (2018) and Schrems II (2020), which invalidated the EU–US Privacy Shield; vendors rolled out regional hosting, Standard Contractual Clauses, customer-managed keys, and stricter telemetry controls. The maker ecosystem faced its own norms test when MakerBot/Thingiverse licensing controversies (post-Stratasys acquisition under Bre Pettis) rekindled debates on Creative Commons usage and ethical reuse. Collectively, these pressures forced the industry to treat platform decisions—region pinning, retention policies, and moderation—as core governance features, not checkboxes. From enterprise PLM to community repositories, the message converged: the model is powerful, and power demands accountable stewardship.Policy, Standards, and Technical Responses that Emerged
Frameworks and standards that encode meaning and responsibility
Mature governance coalesced around a web of standards that express both technical fidelity and organizational duty. ISO 10303 STEP AP242 became the workhorse for managed model-based 3D engineering, combining geometry with semantic PMI, assembly structures, and validation properties to test round-trip integrity. ISO 10303 AP239/PLCS extends that discipline over lifecycle support, managing configuration, maintenance states, and through-life records. ASME Y14.41 formalizes digital product definition so that a model’s tolerances and datum schemes are legally intelligible without drawings. In defense contexts, MIL‑STD‑31000B clarifies data packages and deliverables for MBD regimes, while LOTAR International specifies long-term archiving and retrieval practices to ensure interpretability decades out. ProSTEP iViP and PDES, Inc. publish pragmatic guidance for process maturity, neutral format use, and supplier collaboration; JT Open and 3D PDF ecosystems address lightweight visualization, sometimes paired with rights management. Regulatory anchors meanwhile harden obligations. GDPR and CCPA govern personal and behavioral data associated with scans, telemetry, and collaboration logs; ITAR/EAR and sanctions regimes set red lines for design dissemination and require platform-level controls to avoid prohibited exports. For U.S. defense contractors, NIST SP 800-171/172 and the CMMC program link cybersecurity controls to eligibility, making encryption, logging, and incident reporting non-negotiable in CAD/PLM contexts. In the built environment, ISO 19650 extends information management for BIM, formalizing common data environments and role-based access. Looking ahead, the emerging EU AI Act will intersect with CAD as generative design, topology optimization, and ML-driven assistants enter the workflow; disclosures about datasets, constraints, and risk classification will become part of engineering change governance. The throughline is clear: standards encode the semantics; regulations encode the boundaries; together they transform “good practice” into verifiable responsibility.- AP242 + Y14.41 enables semantic, testable MBD across enterprise boundaries.
- LOTAR demands durability: meaning must survive decades and tool migrations.
- GDPR/CCPA and ITAR/EAR require region-aware storage and controlled sharing.
- NIST/CMMC ties cybersecurity to business eligibility for sensitive programs.
Enterprise policy patterns that consistently work
Enterprises that avoid recurring governance fires converge on similar patterns. First is the single source of authority: designate which object is the master (native CAD, AP242, or a model server record), embed semantic PMI, and enforce change control with effectivity and configuration baselines. Every change is a transaction with approvals, linked requirements, and automated checks for units, materials, and tolerances. Second is supplier onboarding and certification: partners align on tool versions and kernels; they qualify neutral formats (AP242, sometimes JT with mapping tables); and they accept automated conformance checks during import/export. PLM captures an explicit capability matrix for each supplier so workflows can choose exchanges that preserve intent while meeting regulatory restrictions. Access control modernization is the third pillar. Role- and attribute-based access combine to deliver least-privilege: a supplier may view a single subassembly with PMI but not export native files; an auditor may open a 3D PDF/A with watermarked context; a design lead may approve exports only after an ITAR classifier runs. Customer-managed keys, regional pinning, and dual-control for high-risk actions (four-eyes) reduce trust in any single admin. Finally, provenance and audit close the loop: digital signatures at release, hash-based integrity checks for files and derived viewables, tie-back to requirements via ReqIF, and maturity statuses that reflect readiness (concept, preliminary, released, as-built, as-maintained). These patterns work because they acknowledge reality: complex, distributed engineering needs both speed and guardrails. Good policy gives teams a paved road—fast, safe, and instrumented—rather than a maze of manual exceptions.- Authority: master model designation, semantic PMI, controlled effectivity.
- Supplier conformance: versions aligned, AP242 qualified, automated gates.
- Access: attribute-based scopes, region pinning, customer-managed keys.
- Provenance: digital signatures, watermarking, hash integrity, ReqIF linkage.
Platforms and toolchains that operationalize governance
PLM/PDM platforms have evolved from vaults into engines of policy. PTC Windchill, Siemens Teamcenter, Dassault’s ENOVIA/3DEXPERIENCE, Aras Innovator, and Autodesk Vault/ACC now orchestrate workflows with e-signatures, lifecycle states, and disposition histories that satisfy auditors while keeping engineers in flow. CAD itself has become a policy enforcer: model-based definition with semantic GD&T enables downstream automated checks; unit and material consistency can be verified before release; and simulation templates capture solver assumptions to avoid silent divergences. Vendors embed validation: Creo’s MBD annotations, NX PMI, CATIA’s FTA, and Inventor’s MBD extensions all strive to make machine-readability the default so translation and long-term archiving retain meaning. Secure collaboration options have multiplied. Onshape’s document sharing pioneered fine-grained, view-only cloud access with versioned history by design; 3DEXPERIENCE, Teamcenter Active Workspace, and Autodesk cloud services offer scoped links, watermarking, redaction, timeboxed access, and export pre-checks, including ITAR-aware classifiers. Virtual “air-gapped” review sessions, where reviewers interact with streamed pixels rather than receiving files, are increasingly common in defense and high-IP contexts. Long-term archiving has matured: STEP AP242 with validation properties, 3D PDF/A for human-legible records, neutral tessellations for visualization, and planned migration routines with verification to preserve signatures and provenance. Finally, the rise of AI in CAD has pushed data ethics to the fore. Generative design and topology optimization depend on training corpora and constraints; responsible platforms offer opt-in telemetry, on-device options for sensitive organizations, dataset curation tools, and disclosure mechanisms so that engineers know what the machine is optimizing for—and why. The goal is simple: make the ethical choice the easy choice by baking it into the default toolchain.Conclusion
Failures forged the most durable gains
The industry’s most enduring governance lessons were forged in fire. Interoperability crises, unit mismatches, IP leaks, and legal collisions each exposed a different seam where digital intent could unravel. The Boeing 777 moment crystalized digital mock-up as authority, giving rise to PLM-era change control; the Airbus A380 wiring turmoil proved that tool version drift and poor translation governance can sink schedules and trust; NASA’s Mars Climate Orbiter loss made metadata governance, verified requirements flow-down, and unit checks household concepts among CAD/CAE teams. The Waymo v. Uber litigation accelerated DLP and forensic logging; defense supply-chain intrusions made NIST SP 800‑171/172 and CMMC practical necessities; GDPR and Schrems II turned “where is it stored?” into a first-class design decision; export-control tangles around 3D-printed weapons forced platforms to discover their enforcement muscles. Each incident left behind not only scars but also new muscle memory—standards, policies, and platform features—that elevated the baseline. Looking across vendors—Dassault Systèmes, Siemens, PTC, Autodesk, Aras—and the standards community—ISO, ASME, LOTAR International, ProSTEP iViP, PDES, Inc., NIST—the tacit consensus is visible: verifiable semantics, controlled access, and durable archives are non-negotiable. Leaders like Bernard Charlès, Tony Hemmelgarn, Jim Heppelmann, Andrew Anagnost, and Jon Hirschtick have championed openness where possible and responsible control where necessary. The industry’s center of gravity has shifted from file stores toward traceable, policy-aware, model servers that make governance a runtime property rather than a paperwork exercise. That shift is a win for ethics as much as for efficiency.What effective CAD ethics looks like in practice
Effective CAD ethics lives at the intersection of clarity, verification, and control. It starts with clear authority and provenance: the team knows which object is the master; signatures and hashes make that state testable; and requirements link directly to features and annotations. It continues with verified semantics and interoperable exchanges: PMI is not a picture but a machine-readable contract; AP242 and JT with validation properties are employed thoughtfully; and toolchains ship with regression tests for translation fidelity. It incorporates strong, auditable access controls across distributed supply chains: role- and attribute-based scopes, timeboxed and watermarked shares, export pre-checks that include export-control classifiers, and immutable logs that make investigators’ lives easier while signaling to would-be leakers that visibility is high. Compliance-by-design rounds it out. Privacy regimes (GDPR/CCPA) inform where collaboration happens and which telemetry is collected; export controls (ITAR/EAR) dictate who can access what and from where; defense requirements (NIST/CMMC) compel encryption, incident reporting, and regular assessments. None of this should slow engineers to a crawl; rather, the right defaults and the right UX make policy-conforming work the fastest path. A mature organization treats governance gates like unit tests for code: automated, fast, and trusted. That mindset—the engineering of ethics—turns compliance into capability, enabling faster onboarding of partners, safer adoption of AI, and fewer unpleasant surprises in certification, audits, or courtrooms.Near-term imperatives and an ethos for the next decade
The next wave of capability will hinge on how we integrate AI with responsibility, codify supplier conformance, and invest in longevity. AI-assisted modeling is safety- and IP-relevant. Training data must be curated, constraints documented, and explanations available when designs affect regulated domains. Opt-in telemetry, on-device options, and dataset provenance should be first-class controls, not footnotes. Supplier conformance should be codified and continuously verified: tool versions, neutral format qualifications, and security posture captured in PLM; automated gates run on every exchange; nonconformances result in immediate scoped quarantines rather than finger-pointing. Longevity deserves budget: LOTAR-aligned archives, periodic format validation, signature-preserving migrations, and retention policies bound to product liability and certification windows. An actionable checklist for the near term:- Adopt AP242 with validation properties for primary exchanges; require semantic PMI at release.
- Implement attribute-based access, customer-managed keys, and region pinning in all collaboration.
- Run automated unit/material/metadata checks at every lifecycle state change; block on failures.
- Integrate export-control classifiers and CUI tagging into export workflows with four-eyes approval.
- Stand up a LOTAR playbook: archive formats, verification routines, and scheduled migrations.
- Govern AI: curate datasets, document constraints, provide explainability for safety-relevant outputs.
Also in Design News

Real-Time Collaboration Metrics for Design: Taxonomy, Instrumentation, and Governance
February 27, 2026 12 min read
Read More
Cinema 4D Tip: Redshift SSS in Cinema 4D — Scale, Radius & Lighting
February 27, 2026 2 min read
Read More
V-Ray Tip: Export Equirectangular HDRIs from the V-Ray Frame Buffer
February 27, 2026 2 min read
Read MoreSubscribe
Sign up to get the latest on sales, new releases and more …


